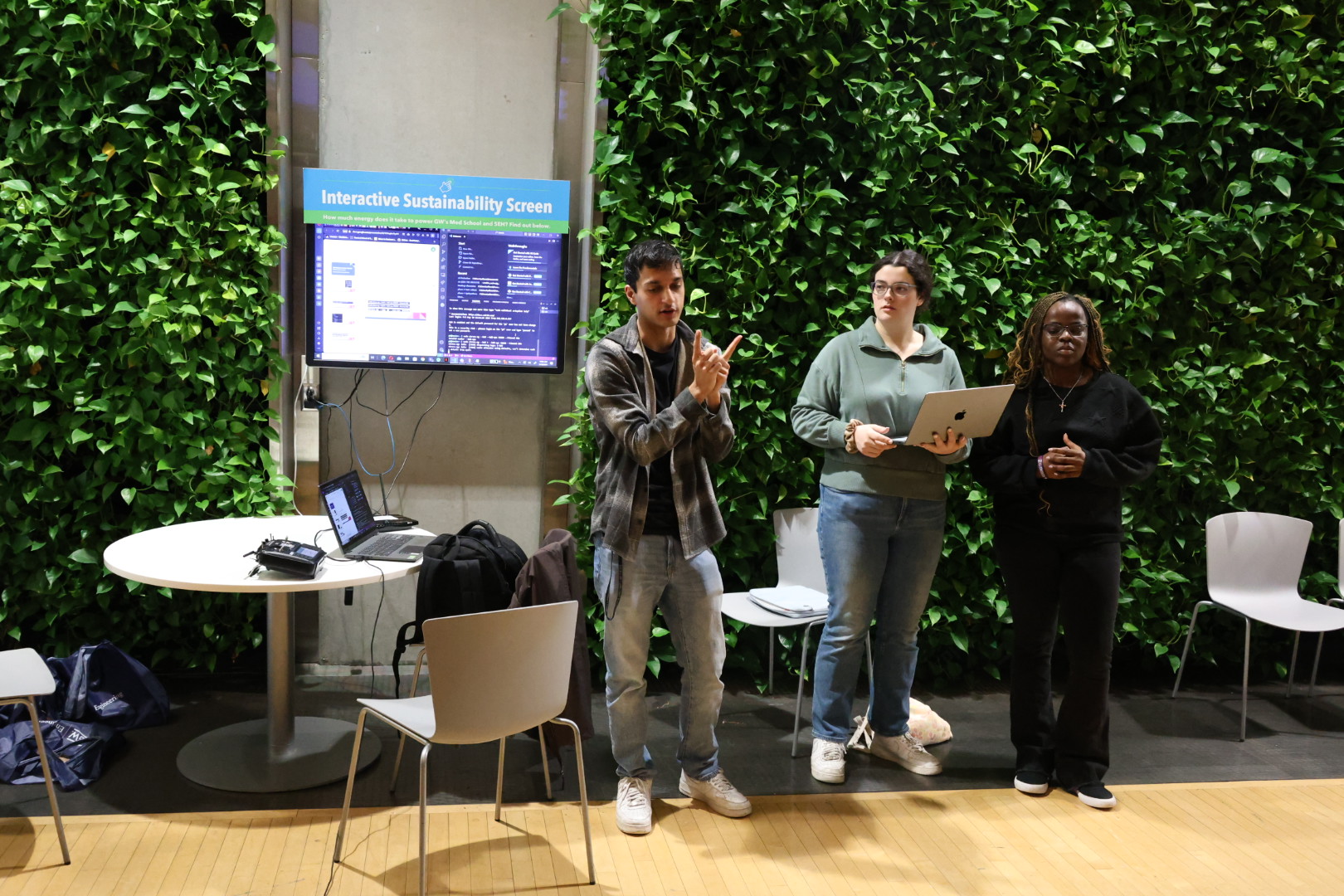
Autonomous cars, unmanned vehicles, and robots are examples of emerging autonomous systems that are becoming more widespread in society, making the security of these systems a top priority. To teach students about security issues in such systems, both attacks and defenses, as well as the hardware designs of such systems, computer science (CS) students in associate professor Sibin Mohan’s class, Secure Autonomous Systems, were tasked with designing and launching security attacks against an autonomous rover that they presented on May 10 in the Science & Engineering Hall.
In their demonstrations, students used their rovers to complete a basic autonomous mission of creating a path in a pizza slice formation, ideally in a continuous loop, while fighting against attacks and explaining their methods. They were required to respond to two types of attacks: controller and timing attacks. In a controller attack, hackers access a system’s controller to manipulate it by zeroing it out, causing the entire system to stop. A timing attack doesn’t require access to the controller but, according to Mohan, is harder to accomplish. In such attacks, hackers overload the systems using various ingenious methods such as excessive computation, overloading buffers or even communication channels, so the controller glitches severely.
The demonstration served as the student’s final exam. For extra credit, they could present mathematical proofs showing that the computations they used were optimal. Sam Haque, the teaching assistant for the course, emphasized the difficult nature of autonomous systems, especially while dealing with the fickle nature of hardware, making this project valuable for students in learning how to deal with that complexity and secure the system.
“The purpose of this project is to teach them how challenging it is to deal with hardware because these are CS students who haven’t worked with hardware before, so through this course and project, they learn how it is painful and often unpredictable,” said Haque.
Junior Olamide Treasure Oluwalade echoed Haque’s sentiments, acknowledging that she learned hardware is difficult, but also expressed: “It was a good experience to learn about real-time systems and the security behind them to fight against attacks.”